wp22245545
-
Secure Boot Explained: A Guide to Protecting Your PC
Secure Boot Secure Boot is a security feature embedded in modern computer systems (powered by UEFI…
-
Understanding Cryptocurrency: A Comprehensive Overview
Cryptocurrency Definition: A cryptocurrency is a digital or virtual currency that uses cryptography for security, operates…
-

Extend IDE Power Connections with this Y Splitter
Interface port: One side is large 4 Pin IDE male connector, and the other side is…
-
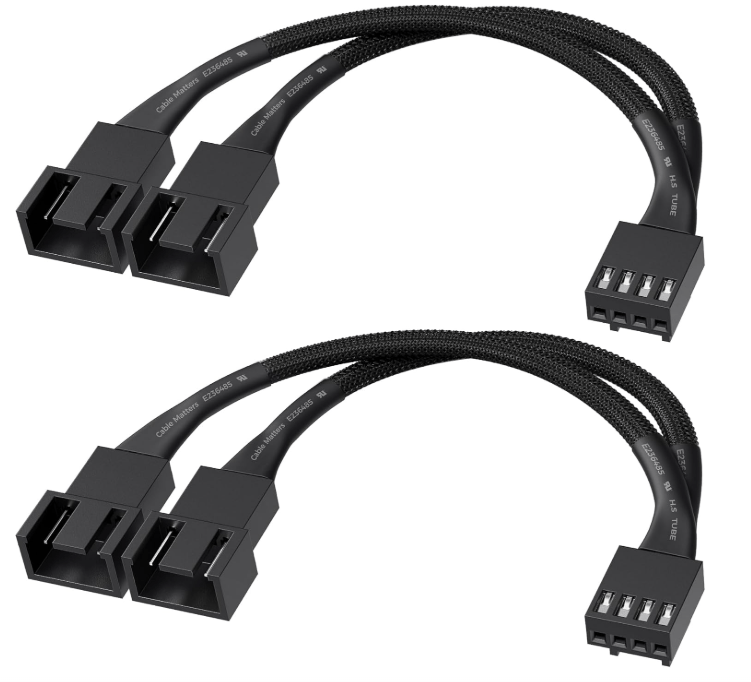
Boost Your PC’s Airflow with a Dual Fan Splitter
Dual Fan Connection: This PC fan splitter Y cable connects 2 computer case fans to a…
-

Maximize PC Cooling with 4-Pin Fan Splitter Cable
4Pin 1 to 4 Ways PWM Fan Splitter Cable, to realize 4 fans powered by 1…
-
Certificate Authority: Ensuring Secure Digital Communications
A Certificate Authority (CA) is a trusted third-party organization or entity that issues digital certificates to…
-
Understanding SSL Certificates: A Complete Guide
SSL Certificate Definition: An SSL (Secure Sockets Layer) Certificate (now commonly referring to its successor, TLS—Transport…
-
TLS 1.3 Handshake Explained: A Guide
TLS Handshake Basic Definition The TLS (Transport Layer Security) Handshake is a cryptographic process that establishes a secure,…
-
VPN Tunnel Basics: Security and Protocols Explained
VPN Tunnel (Virtual Private Network Tunnel) Definition A VPN Tunnel is an encrypted, secure communication pathway that connects…
-
Understanding Proxy Chaining: A Comprehensive Guide
Proxy Chaining 1. Basic Definition Proxy Chaining (or “proxy cascade”) is a network technique where multiple proxy…